In the ecosystem of blockchain technology, maintaining the integrity and security of the network is paramount. This is especially true for Proof of Stake (PoS) networks, where the concept of "slashers" comes into play. Unlike the physical world's police or regulatory bodies, blockchain networks rely on algorithmic mechanisms to enforce rules and deter bad actors. Among these mechanisms, slashers are pivotal in preserving the trust and functionality of PoS networks. Let's delve into what slashers are, how they work, and their importance in the blockchain landscape.
What Are Slashers?
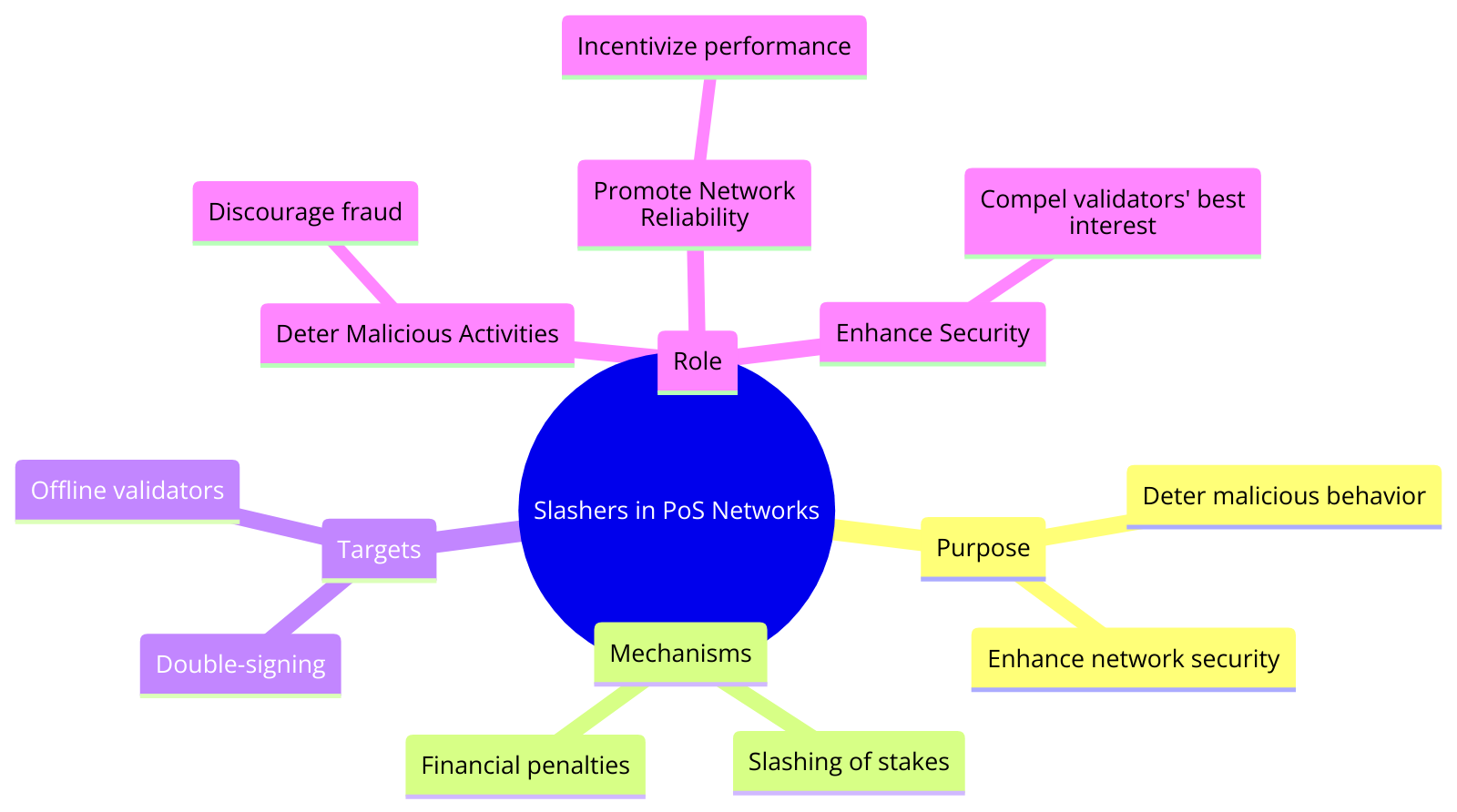
Slashers are specific mechanisms within PoS blockchain networks designed to penalize validators who act maliciously or fail to comply with the network's protocols. These penalties often involve the "slashing" (forfeiture) of a portion of the stake that validators have committed as collateral to participate in the network's consensus process. The primary aim is to deter behaviors that could harm the network, such as double-signing blocks or being offline during crucial validation periods.
The Role of Slashers
- Deterring Malicious Activities: By imposing financial penalties, slashers discourage validators from engaging in activities that threaten the network's security, such as attempting to validate fraudulent transactions.
- Promoting Network Reliability: Validators are incentivized to maintain a high level of performance and reliability; those who frequently go offline or fail to validate transactions correctly risk being slashed.
- Enhancing Security: The threat of being slashed compels validators to act in the network's best interest, bolstering the overall security and robustness of the blockchain.
Examples of Slashers in Action
- Ethereum 2.0: With its transition to a PoS consensus mechanism, Ethereum 2.0 introduces slashing conditions to penalize validators for actions like equivocation (double voting) and being offline, ensuring the network's security and integrity.
- Cosmos: The Cosmos network employs a slasher mechanism where validators can be slashed for double signing or prolonged downtime, incentivizing active and honest participation in the consensus process.
- Polkadot: Polkadot's Nominated Proof of Stake (NPoS) system also includes slashing to punish security breaches, protecting the network from attacks and encouraging validator diligence.
Challenges Arising From Excessive Slashing
While slashing is effective in deterring malicious behavior and ensuring validator compliance, it's not without its challenges. Excessive slashing could deter potential validators from participating due to the high risk, potentially leading to centralization as only large, well-capitalized entities can afford to risk participation. Furthermore, the parameters around slashing conditions need to be carefully calibrated to be fair yet sufficiently deterrent.
A Security and Integrity Framework of PoS
Slashers are an essential component of the security and integrity framework of PoS blockchain networks. By providing a mechanism to penalize non-compliant or malicious validators, slashers help ensure that PoS networks remain secure, reliable, and trustworthy. As blockchain technology continues to evolve, the role of slashers and the principles behind them will undoubtedly adapt, maintaining their crucial position in the ecosystem's defense against threats and misbehavior.
Join the Colony Community
Stay connected and dive deeper into the world of on-chain organizations with Colony. For the latest updates, insights, and discussions, follow us on our community channels:
- Website: Visit our website
- Twitter: Follow us on Twitter
- Discord: Join our Discord community
- Github: Find Colony on Github
Together, let's build the future of decentralized collaboration.